
WannaCry? How to Prevent Your Data
Carlo Espiritu, Principal, Triple Point Security
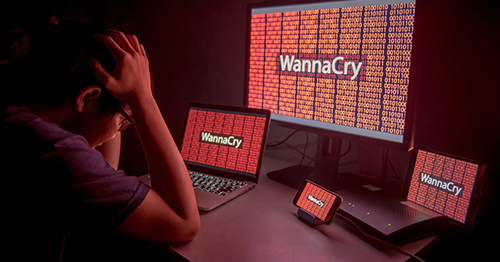
Regardless of which circles you run in, cybersecurity and cloud security events permeate our lives. In May, the WannaCry ransomware infected over 200,000 computers across the globe, disrupting healthcare, telecommunications, transportation, among other industries. There are ongoing investigations for alleged state-sponsored cyber attacks designed to meddle with last year’s US presidential election. Most recently, we’ve heard, on a number of occasions, where cloud services weren’t properly secured and left sensitive information exposed to the Internet.
While we’ve seen similar occurrences with the former two scenarios, the latter scenario is an example of fundamental security principles being overlooked due to unfamiliarity with the cloud service and/or unfamiliarity with security technology used to identify and secure it. We are huge proponents of cloud services; they are flexible, cost-effective, and extremely powerful, allowing anyone to create enterprise-class infrastructures in a matter of minutes or utilize enterprise-grade applications for very reasonable prices.
More and more organizations are venturing into the cloud, and we encourage it. We also encourage engaging with your cloud service provider (CSP) and reference the numerous resources that they have available, such as blogs, videos, and whitepapers. There are also numerous leading-edge security technologies to help gain visibility and control over cloud services, such as cloud access security brokers (CASBs), tenant monitoring solutions, and network visibility platforms. Embracing cloud services must include the application of fundamental security concepts and principles to cloud services, just like any IT; it should also include embracing the leading-edge security technologies that secure them.
Thank you to the GovCon committee for keeping us informed on the most up-to-date information on protecting our data online. To get more involved in the GovCon committee, click here.
